Published: November 17, 2023
Security 3-2-1 Week of 11/17/23
By Annie articles
3 Interesting Articles
ChatGPT: OpenAI Attributes Regular Outages to DDoS Attacks
Dark Reading: The AI application ChatGPT faced repeated outages this week, with disruptions attributed to a distributed denial of service (DDoS) attack impacting its interface and API. OpenAI, the developer behind ChatGPT, identified abnormal traffic patterns indicating the attack and reported major service disruptions starting November 8. The company has since resolved the issue but remains vigilant against future cyberattacks. Experts believe AI platforms, with access to valuable data, are prime targets for cyberattacks aimed at tarnishing their reputation. Defending against sophisticated DDoS attacks requires robust strategies, including multiple layers of security and advanced mitigation techniques. The hacktivist group Anonymous Sudan claimed responsibility for the DDoS attack, citing political and religious motives and affiliations with other hacking groups. The group has previously targeted various Israeli websites and entities, indicating a pattern of politically motivated cyberattacks.
McLaren Health Care says data breach impacted 2.2 million people
Bleeping Computer: McLaren Health Care, a non-profit healthcare system, has announced a data breach affecting nearly 2.2 million individuals. This breach, occurring between late July and August 2023, compromised sensitive personal information including names, Social Security numbers, health insurance details, dates of birth, billing information, medical records, and more. Although there’s currently no indication that the exposed data has been misused, McLaren is advising those affected to monitor their financial accounts and benefit statements closely. Notably, the ALPHV/BlackCat ransomware group claimed responsibility for the attack, threatening to auction the stolen data which they allege affects 2.5 million people. McLaren’s network includes 14 hospitals and a large workforce, emphasizing the significant impact of this breach.
8 reasons your cybersecurity training program sucks and how to fix it
CSO: Cybersecurity training programs often fail to engage employees due to outdated content and uninspiring methods. Experts recommend a more interactive approach, such as realistic simulations and role-playing, tailored to specific roles and technologies. Regular updates with the latest threats and varied delivery methods that cater to individual risk profiles are crucial. Gamification and practice-based learning can enhance engagement and skill acquisition. Effective training should also be impactful and transferable, focusing on developing a robust security culture through diverse training methods. Immediate feedback on actions and continuous conversation about cybersecurity within the organization are essential to keep training relevant and integrated into the business context. This approach not only improves learning but fosters a proactive security culture.
2 Stats You Should Know
Nearly three-quarters (72%) of IT and security decision-makers reported are concerned about the potential adverse effects of generative AI on their organization’s cybersecurity. (source)
In 1995, Christopher Pile became the first person to be jailed in the UK for writing and distributing a computer virus. Pile was sentenced to 18 months for 11 offenses. He wrote and distributed the Pathogen and Queeg viruses, as well as the virus cloaker, Smeg. (source)
1 More Thing
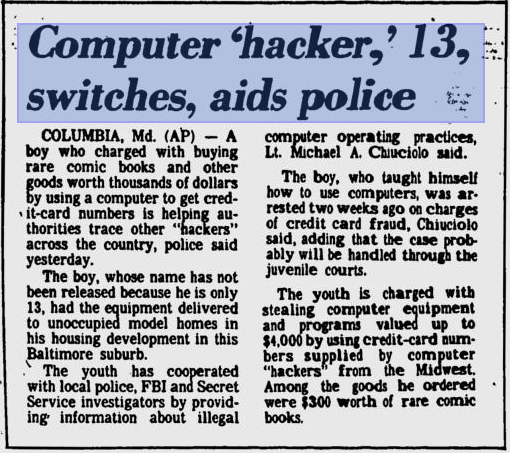
Anyone know what happened to this kid?
“Computer ‘hacker,’ 13, switches, aids police” – Pittsburgh Post-Gazette, 1st September, 1984